Why Law Firm Cybersecurity Best Practices Can’t Wait
Law firm cybersecurity best practices are the specific steps legal practices must take to protect sensitive client data, meet ethical obligations, and avoid devastating breaches.
Here’s a quick overview of the most essential ones:
| Best Practice | Why It Matters |
|---|---|
| Multi-factor authentication (MFA) | Blocks 99%+ of credential-based attacks |
| Data encryption (in transit + at rest) | Protects data even if systems are compromised |
| Employee phishing training | Addresses the #1 cause of breaches |
| Strong passwords + password manager | Eliminates weak or reused credentials |
| Regular data backups (offline + encrypted) | Enables recovery without paying ransom |
| Incident response plan | Reduces damage and downtime after an attack |
| Third-party vendor vetting | Closes back-door entry points |
| Role-based access controls | Limits exposure if one account is compromised |
| VPN + secure remote access | Protects data outside the office |
| Cyber liability insurance | Covers costs when other measures fall short |
| Regular risk assessments + penetration testing | Finds vulnerabilities before attackers do |
| Software updates + patch management | Closes known security gaps |
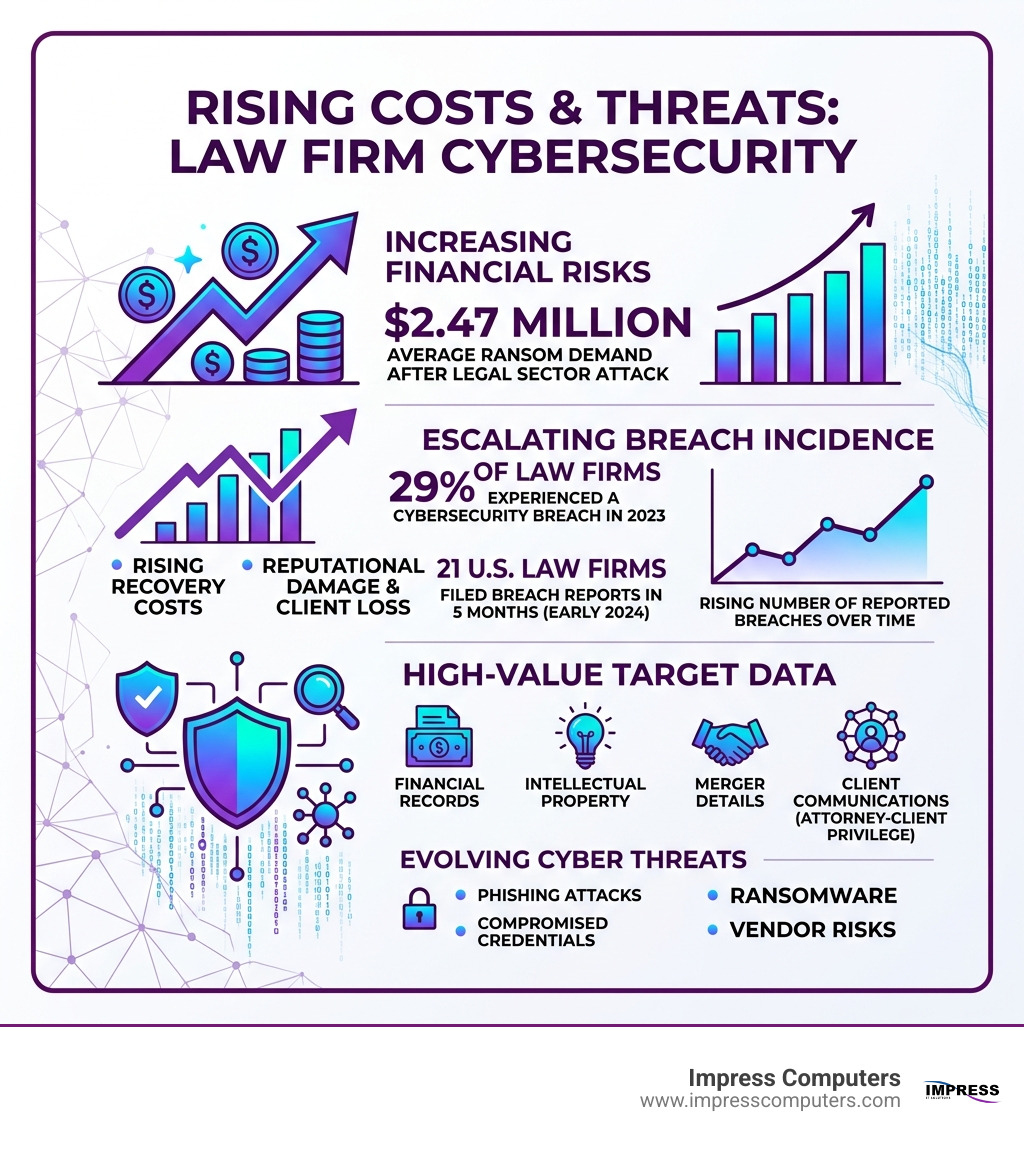
The stakes are high. 29% of law firms experienced a cybersecurity breach in 2023. The average ransom demand following a legal sector attack is $2.47 million. And in just the first five months of 2024, 21 U.S. law firms filed data breach reports with state attorneys general — nearly matching the total for all of the prior year.
Law firms hold some of the most sensitive data that exists: financial records, intellectual property, merger details, medical information, and communications protected by attorney-client privilege. That makes them an attractive target — and a vulnerable one, especially when cybersecurity isn’t treated as a core business priority.
As one cybersecurity expert put it plainly: cybersecurity for law firms is more than a technical issue — it’s a matter of trust and professional integrity.
I’m Roland Parker, founder and CEO of Impress Computers, a managed IT services and cybersecurity firm that has helped Houston-area businesses — including legal practices — build secure, compliant infrastructure since 1993. My experience working with professional services firms is the foundation for everything I’ll cover in this guide to law firm cybersecurity best practices.
Why Law Firms are Prime Targets for Cybercriminals
It’s a common misconception among smaller firms in places like Katy or Sugar Land that they are “too small to be noticed” by hackers. In reality, the legal industry is a gold mine for cybercriminals. Law firms act as central repositories for high-value data that can be monetized in dozens of ways.
Whether you are a solo practitioner in Richmond or a mid-sized firm in The Woodlands, you likely handle:
- Personally Identifiable Information (PII): Social Security numbers, birthdays, and addresses.
- Protected Health Information (PHI): Medical records used in personal injury or malpractice suits.
- Intellectual Property (IP): Trade secrets and patent filings.
- M&A Details: Non-public information about upcoming mergers or acquisitions that is ripe for insider trading or extortion.
According to research on Data Security and Privacy Implications in Law Firms, the sheer volume of this data makes firms “one-stop shops” for identity thieves. Furthermore, Common IT Problems for Legal Firms and How to Solve Them often stem from the fact that legal professionals prioritize billable hours over system updates, leaving digital “back doors” wide open.
Threat actors use ransomware to lock you out of your case files, phishing to trick your paralegals into giving up passwords, and sometimes even exploit insider threats—disgruntled or careless employees who bypass security protocols. When a firm is hit, the damage isn’t just financial; it’s a breach of the sacred client-attorney privilege.
Ethical and Legal Obligations for Data Protection
In the legal world, cybersecurity isn’t just a “good idea”—it’s a professional requirement. The American Bar Association (ABA) has been very clear about this. ABA Model Rule 1.6(c) requires lawyers to make “reasonable efforts” to prevent the unauthorized disclosure of, or unauthorized access to, information relating to the representation of a client.
But the buck doesn’t stop with the ABA. Depending on your practice area and where your clients are located, you may be subject to:
- GDPR: If you handle data for EU citizens.
- CCPA/CPRA: If you have clients in California.
- HIPAA: If you handle health records (common in personal injury or healthcare law).
- State-specific laws: Texas has its own data breach notification requirements that you must follow if a Houston resident’s data is compromised.
Failing to meet these standards can lead to more than just a fine. It can result in malpractice suits, loss of your license to practice, and irreparable damage to your reputation. As noted in Best Practices for Law Firms to Meet Cybersecurity Obligations, staying compliant is a moving target. This is why many firms in the Houston area turn to IT Managed Services for Law Firms – Protecting Clients, Compliance, and Productivity to ensure their technical safeguards match their legal obligations.
12 Essential Law Firm Cybersecurity Best Practices
Building a “bulletproof” policy starts with a layered defense. No single tool can stop every attack, but these 12 law firm cybersecurity best practices create a formidable barrier.
- Multi-factor Authentication (MFA): This is the single most effective tool in your arsenal. Microsoft studies show MFA blocks over 99% of account compromise attacks.
- Data Encryption: Ensure data is encrypted “at rest” (on your servers/laptops) and “in transit” (when being emailed or uploaded).
- Strong Password Policies: Move away from “Password123.” Require complex passphrases of at least 12–14 characters.
- Password Managers: Tools like 1Password or LastPass allow staff to use unique, complex passwords for every site without needing to memorize them.
- Endpoint Detection and Response (EDR): Modern EDR is the “next-gen” version of antivirus. It uses AI to spot suspicious behavior, not just known viruses.
- Secure Remote Access (VPN): If your team works from home in Cypress or a coffee shop in Sugar Land, a VPN creates an encrypted tunnel for their data.
- Regular Data Backups: We recommend the 3-2-1 rule: 3 copies of your data, on 2 different media types, with 1 copy stored offline (immutable) to prevent ransomware from deleting your backups.
- Employee Awareness Training: Your staff is your weakest link—or your first line of defense.
- Incident Response Plan (IRP): You need a written “fire drill” for what happens if a breach occurs.
- Third-Party Vendor Vetting: Ensure your cloud providers (like Clio or NetDocuments) meet high security standards.
- Network Segmentation: Keep your guest Wi-Fi separate from your internal server network.
- Regular Risk Assessments: You can’t fix what you don’t know is broken.
For a deeper dive, the Law Firm Cybersecurity Best Practices Guide offers excellent insights into how these tools integrate with legal software. Many firms find that Common IT Problems Law Firms Face in Cypress TX and How Managed IT Services Solve Them are easily mitigated once these 12 pillars are in place.
Implementing Technical Law Firm Cybersecurity Best Practices
The “technical” side of security is where the heavy lifting happens. At Impress Computers, we focus on creating a “Zero Trust” environment. This means the network trusts no one by default, whether they are inside or outside the office.
- VPNs & Secure Wi-Fi: Never allow staff to access client files over public Wi-Fi without a VPN. Even in your own office, ensure your Wi-Fi uses WPA3 encryption.
- Network Segmentation: If a hacker gets into a printer or a smart thermostat, segmentation prevents them from jumping over to your server where the sensitive M&A files live.
- AI-Driven Security: We use self-learning AI tools that monitor network traffic 24/7. If a paralegal suddenly starts downloading 5,000 files at 3:00 AM, the AI recognizes this as an anomaly and kills the connection instantly.
This level of technical oversight is Why Law Firms Depend on Reliable Help Desk IT Services—it allows attorneys to focus on the law while the technology handles the defense.
Operational Law Firm Cybersecurity Best Practices
Technology is only half the battle. The “human element” is often where the most sophisticated technical defenses fail.
- Employee Training & Phishing Simulations: We recommend mandatory annual training combined with quarterly “fake” phishing emails. If an employee clicks the link in a simulated test, they get immediate, non-punitive “just-in-time” training.
- Incident Response Plans (IRP): An IRP should include a designated team (IT, Legal, HR, Management) and clear steps for containment and notification. Don’t wait for a crisis to decide who has the authority to shut down the server.
- Third-Party Vendor Vetting: Before signing up for a new e-discovery tool, ask for their SOC 2 report. Your security is only as strong as the weakest vendor you trust with your data.
The Cybersecurity Toolkit for In-house Lawyers is a fantastic resource for managing these operational risks. It’s also vital to understand Why Most IT Providers Fail Law Firms – And What to Look For Instead; generic IT support often misses the specific ethical and confidentiality workflows unique to the legal profession.
Risk Management: Audits, Insurance, and Resilience
A bulletproof policy requires ongoing maintenance. This is where Risk Management comes in. Think of it as a physical for your firm’s health.
- Penetration Testing & Vulnerability Scans: A “Pen Test” is an authorized simulated attack on your firm. It’s the only way to know for sure if your defenses actually work.
- Cyber Liability Insurance: Even with the best defenses, things can go wrong. A standalone cyber policy can cover the costs of forensics, legal fees, notification costs, and even public relations efforts to save your reputation.
- Business Continuity: If a hurricane hits Houston or a ransomware attack wipes your server, how fast can you be back up and running? A true business continuity plan ensures you can access your files and bill your hours within minutes, not weeks.
When considering the cost of these measures, look at Managed IT Services Pricing for a 40-Person Legal Firm to get a realistic idea of the investment required to stay secure. Knowing How to Choose the Best Legal IT Services in Houston will help you find a partner who understands that for a law firm, “down time” is “lost revenue.”
Frequently Asked Questions about Law Firm Cybersecurity
What are the most common cyber threats facing law firms?
The “Big Three” are Ransomware, Phishing, and Business Email Compromise (BEC). In BEC attacks, a hacker gains access to an attorney’s email and sends “updated” wiring instructions to a client during a real estate closing. These are devastating because they rely on the client’s trust in the attorney. Insider threats and supply chain attacks (where a vendor like a file-sharing service is breached) are also rising rapidly.
How often should law firms conduct cybersecurity training?
We recommend annual mandatory training for all staff, including partners. However, “one and done” isn’t enough. Quarterly phishing simulations keep security top-of-mind. Furthermore, new hires should receive a security briefing on day one as part of their onboarding. Our Help Desk IT Services for Legal Firms in Cypress TX often include these training modules as part of our standard support.
Is cyber insurance mandatory for legal practices?
While not technically “mandatory” by law in Texas, it is often a requirement in client contracts, especially for corporate or government clients. Ethically, you have a duty to protect client data, and having the financial means to recover from a breach is a key part of that responsibility. Many firms face Common Challenges Facing Law Firms in The Woodlands when they realize their general liability policy doesn’t cover digital theft. A standalone cyber policy is highly recommended.
Conclusion
Building a bulletproof law firm cybersecurity policy isn’t a weekend project—it’s an ongoing commitment to your clients and your firm’s future. In an era where 29% of firms are being breached, “hoping for the best” is no longer a viable strategy.
At Impress Computers, we specialize in taking the technical burden off your shoulders. We provide managed IT services and top-tier security for law firms across Houston, Sugar Land, Katy, and The Woodlands. We understand that in the legal world, every minute counts, which is why we offer a 15-minute response guarantee and maintain 99.9% uptime for our clients.
Don’t let your firm be the next statistic. Whether you need a full security audit, an incident response plan, or 24/7 monitoring, we are the partner Houston attorneys rely on.