Why Your Business Needs a Cyber Strategy Before the Hackers Do
Why Most Businesses Get Hacked Before They Ever Build a Defense
Cybersecurity consultancy services are specialized advisory and hands-on services that help businesses identify security risks, close vulnerabilities, and build a proactive defense strategy — before an attack happens.
Here’s a quick breakdown of what they typically include:
- Risk assessments — finding gaps in your current security posture
- Penetration testing — simulating attacks to expose weaknesses
- Compliance guidance — aligning with standards like HIPAA, PCI-DSS, and SOC 2
- Security roadmaps — custom plans to improve your defenses over time
- Ongoing monitoring — continuous protection after the strategy is in place
If you run a business in manufacturing, construction, banking, or legal services in Houston, here’s the hard truth: most cyberattacks don’t happen because hackers are sophisticated — they happen because businesses weren’t prepared.
Exposed vulnerabilities are consistently cited as one of the most common root causes of ransomware incidents. And yet, many businesses still treat cybersecurity as an afterthought — something to deal with after a breach, not before.
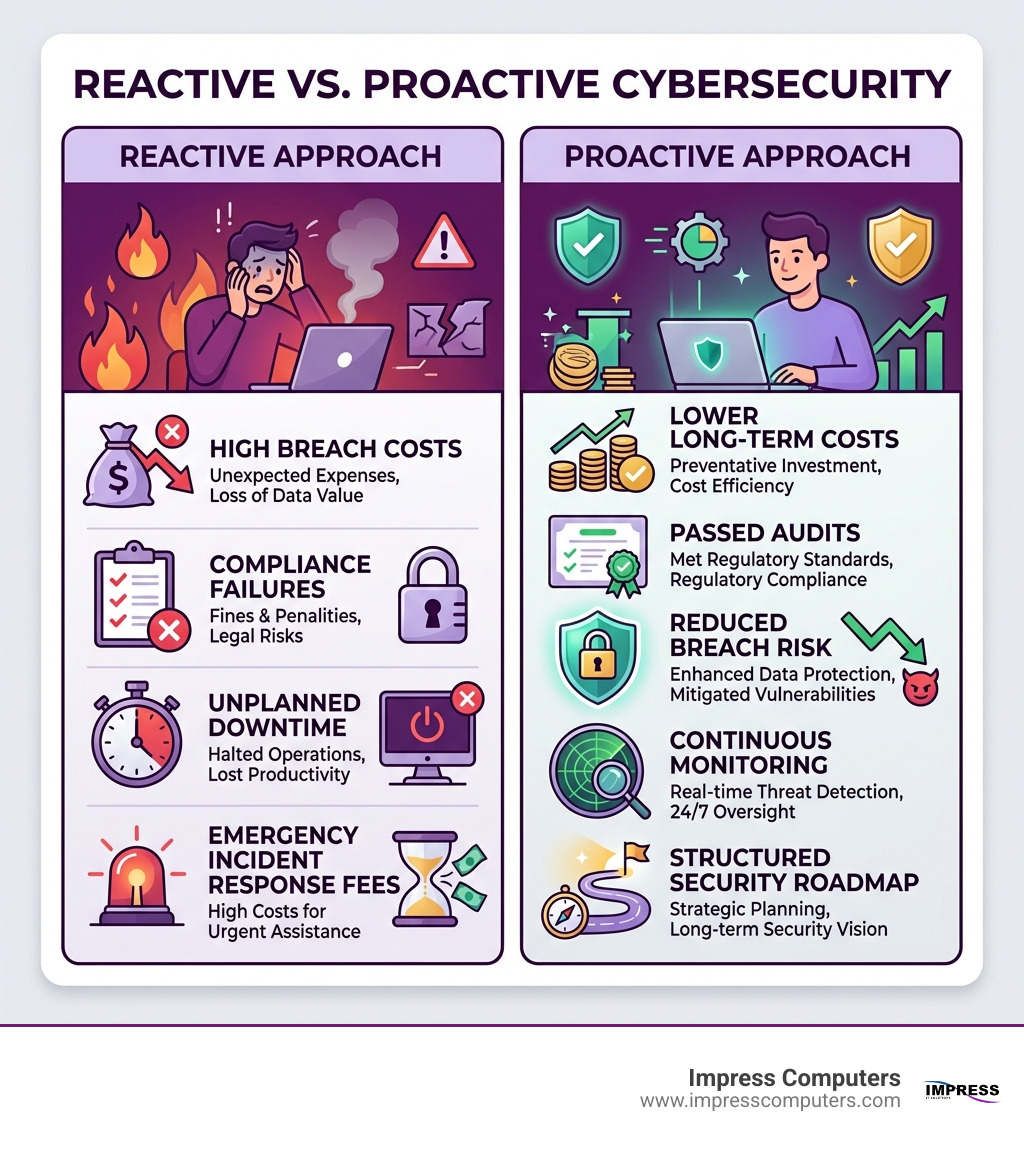
That reactive approach is expensive. Downtime, data loss, regulatory fines, and broken client trust can follow a single incident.
A cybersecurity consultancy helps you get ahead of that. Instead of patching holes after the damage is done, you build a strategy that protects your operations, your clients, and your reputation before hackers find a way in.
The Strategic Value of cybersecurity consultancy services
In the modern digital landscape, simply having a firewall and an antivirus program is like putting a screen door on a vault. It might keep the bugs out, but it won’t stop a determined intruder. This is where the strategic value of cybersecurity consultancy services comes into play. These services move beyond the “install and forget” mentality, focusing instead on building a resilient security architecture that evolves alongside your business.
A startling 2024 Gartner Future of Security Architecture Survey reveals that many organizations fail to seek professional advisory services when establishing their strategic security architecture. This oversight often leads to fragmented defenses that are difficult to manage and easy to bypass. By engaging a consultancy, you gain access to experts who view your business through the lens of risk, helping you prioritize your investments where they matter most.
How cybersecurity consultancy services Differ from General IT Support
We often hear business owners ask, “Doesn’t my IT guy handle security?” While general IT support is essential for keeping your computers running and your printers connected, it is fundamentally different from specialized cybersecurity consultancy.
- General IT Support: Focuses on availability, performance, and day-to-day troubleshooting. They ensure you can access your email and that your software is up to date.
- Cybersecurity Consultancy: Focuses on risk management, threat prevention, and data integrity. They look for the “how” and “why” behind potential breaches.
Think of IT support as the mechanic who keeps your car running, while a cybersecurity consultant is the specialized security team that ensures your armored transport can withstand an ambush. For a deeper dive into these differences, check out our insights on cybersecurity management.
Key Benefits for Small and Medium-Sized Businesses
Small and medium-sized businesses (SMBs) in areas like Katy, Cypress, and Sugar Land are often prime targets for hackers because they are perceived to have weaker defenses. The benefits of hiring a consultancy include:
- Significant Breach Reduction: Proactive patching and configuration can reduce breach risk by as much as 80%.
- Secure Innovation: You can adopt new technologies (like cloud services or AI) with confidence, knowing the risks have been mitigated.
- Stakeholder Trust: Clients and partners are more likely to work with you if you can prove your data is secure.
- Cost Savings: Preventing a breach is always cheaper than recovering from one.
- Resource Optimization: Instead of hiring a full-time CISO (Chief Information Security Officer), you get access to a team of experts for a fraction of the cost.
Core Offerings: Proactive Testing and Risk Mitigation
A high-quality consultancy doesn’t just give you a list of “best practices.” They put your systems to the test. This proactive approach identifies the exact points where a hacker could break in.
| Service | Goal | Methodology |
|---|---|---|
| Penetration Testing | Find specific vulnerabilities | Controlled “hacks” on specific systems or networks. |
| Vulnerability Assessment | Inventory all known risks | Automated scanning and manual review of software/hardware. |
| Red Teaming | Test detection and response | A full-scale, multi-layered simulated attack over time. |
| Adversary Emulation | Mimic specific threat actors | Using the exact tactics, techniques, and procedures (TTPs) of known hacker groups. |
To understand the full scope of these technical tests, you can Download the Sophos Advisory Services brochure for a detailed look at industry-standard methodologies.
Penetration Testing and Vulnerability Assessments
Penetration testing is essentially a “fire drill” for your digital defenses. It uncovers high-severity vulnerabilities that might not be listed in standard databases like the OWASP Top 10. In fact, research shows that many web applications exhibit at least one critical vulnerability that standard tools might miss.
By hardening your network and identifying zero-day flaws (vulnerabilities that the software manufacturer doesn’t even know about yet), we help ensure that your perimeter is solid. If you’re wondering how to tell if your current setup is up to par, read our guide on how to determine if your IT network is secure from attacks. This is a cornerstone of incident prevention—stopping the fire before it starts.
Red Teaming and Adversary Emulation
While a penetration test might look for a “way in,” a Red Team exercise tests your entire organization’s ability to detect and respond to an intruder. This includes social engineering (testing if employees click on phishing links), physical security, and digital detection systems.
These exercises often culminate in tabletop exercises, where your leadership team sits down to walk through a simulated crisis. This ensures everyone knows their role when things go wrong. In the age of AI, these simulations are becoming even more critical, as attackers use AI to craft more convincing scams and automate their attacks.
Navigating Compliance in Regulated Industries
For businesses in Houston’s healthcare, finance, and manufacturing sectors, cybersecurity isn’t just a good idea—it’s a legal requirement. Whether it’s HIPAA for patient data or PCI-DSS for credit card processing, the stakes are incredibly high.
Achieving Regulatory Compliance through cybersecurity consultancy services
Compliance is often seen as a mountain of paperwork, but a good consultancy turns it into a manageable roadmap. We help you align with frameworks such as:
- HIPAA/PHIPA: Protecting sensitive health information.
- PCI-DSS: Ensuring secure credit card transactions.
- SOC 2: Verifying that your service providers manage data securely.
- ISO 27001: An international standard for information security management systems.
Many of our clients in the manufacturing sector specifically look for NIST compliance, which is often required for government contracts. One of the most effective ways to achieve these standards is through a Zero Trust model, where no one is trusted by default, whether they are inside or outside the network.
Industry-Specific Guidance for Houston Businesses
Every industry faces different threats. A law firm in Downtown Houston has different risks than a construction company in Brookshire or a manufacturing plant in The Woodlands.
- Manufacturing: Focuses on protecting intellectual property and preventing operational downtime.
- Legal & CPA Firms: Must protect attorney-client privilege and sensitive financial records.
- Construction: Often deals with transient job sites and the need for IT compliance in construction to secure project bids and blueprints.
- Banking: Requires the highest levels of encryption and fraud detection.
The Methodology: From Discovery to Continuous Monitoring
A successful engagement with a cybersecurity consultancy follows a structured process. It’s not a one-time event, but a continuous cycle of improvement.
Discovery and Security Roadmap Development
The first step is always Discovery. We can’t protect what we don’t know exists. This phase involves:
- Gap Analysis: Comparing your current state to industry benchmarks.
- Identifying “Crown Jewels”: Determining which data is most critical to your business survival.
- Customized Research: Analyzing threat intelligence specific to your industry and location.
- Stakeholder Interviews: Understanding the business goals to ensure security doesn’t get in the way of productivity.
The result is a customized security roadmap—a clear, prioritized plan of action.
Implementation and Ongoing Security Governance
Once the strategy is set, we move to implementation. This might include deploying new endpoint protection, hardening firewalls, or setting up a vCISO (Virtual Chief Information Security Officer) service. A vCISO provides executive-level security leadership without the six-figure salary of a full-time hire.
Continuous monitoring is the final, ongoing piece of the puzzle. Hackers don’t work 9-to-5, and neither should your security. By monitoring for threats 24/7, we can trigger an incident response the moment something looks suspicious.
Choosing the Right Partner for Your Business
Choosing a consultancy is a big decision. You are essentially handing over the keys to your digital kingdom. You need a partner that combines technical depth with local accountability.
Global Players vs. Local Consultancies
There are massive global firms out there, but they often treat SMBs like just another number.
- Global Players: Have deep pockets and massive teams, but their services can be “cookie-cutter” and incredibly expensive.
- Local Consultancies: Offer personalized service, understand the local business environment, and can be on-site in Fulshear or Missouri City within the hour if a physical emergency arises.
Why Local Expertise Matters in the Houston Area
For businesses in the Greater Houston Area, local expertise is invaluable. We understand the specific regulations in Texas and the unique needs of the local economy. Whether it’s rapid response times (like our 15-minute guarantee) or knowing the specific IT challenges of a Houston-based manufacturing plant, being local matters.
When selecting a partner, look for:
- Certifications: Are they certified in the frameworks you need (NIST, ISO, etc.)?
- Response Time: How fast will they help you if you are under attack?
- Sector Knowledge: Do they understand your specific industry?
- Transparency: Do they explain things in plain English, or do they hide behind “tech-speak”?
Frequently Asked Questions about Cybersecurity Consultancy
How much do cybersecurity consultancy services cost?
Pricing varies based on the size of your network, the complexity of your industry (compliance needs), and the depth of testing required. A simple risk assessment for a small firm is much different than a full Red Team exercise for a multi-site manufacturing company. Most consultancies offer tiered pricing or project-based fees.
How often should my business engage a consultant?
At a minimum, you should have a professional risk assessment once a year. However, you should also call your consultant during periods of rapid growth, when implementing new major software, or if there has been a significant change in industry regulations.
What is the difference between a consultancy and a full-service firm?
A consultancy primarily provides strategic advice and testing. A full-service firm (like many Managed Security Service Providers) provides both the strategy and the day-to-day management of the security tools. Many businesses prefer a hybrid approach where they get both high-level strategy and hands-on support from the same trusted partner.
Conclusion
The digital world isn’t getting any safer, but your business can get a lot more resilient. By moving from a reactive “hope for the best” approach to a proactive strategy built on cybersecurity consultancy services, you take control of your company’s future.
At Impress Computers, we’ve spent over 20 years protecting businesses across Houston, from Katy to The Woodlands and everywhere in between. We don’t just fix computers; we secure your livelihood. With our 15-minute response guarantee and 99.9% uptime commitment, we ensure that your technology is an asset, not a liability.
Don’t wait for a ransom note to appear on your screen to start thinking about security. Get expert IT support in Houston today and let’s build a defense that keeps the hackers out for good.